The Next Era of Cyber Security Capabilities
Context is the mortar and AI are the bricks that stand up the new cyber platform
The difference between traditional cybersecurity products and modern cybersecurity platforms lies in the use of context (vs. data) and AI to facilitate more intelligent and accurate decisions.
This wave of change hasn't emerged suddenly; it has been rising and swelling over several years, leading to an inflection point where we witness a drastic shift from the status quo. This new era of cybersecurity capabilities is arriving more swiftly than anticipated, poised to transform daily cybersecurity operations.
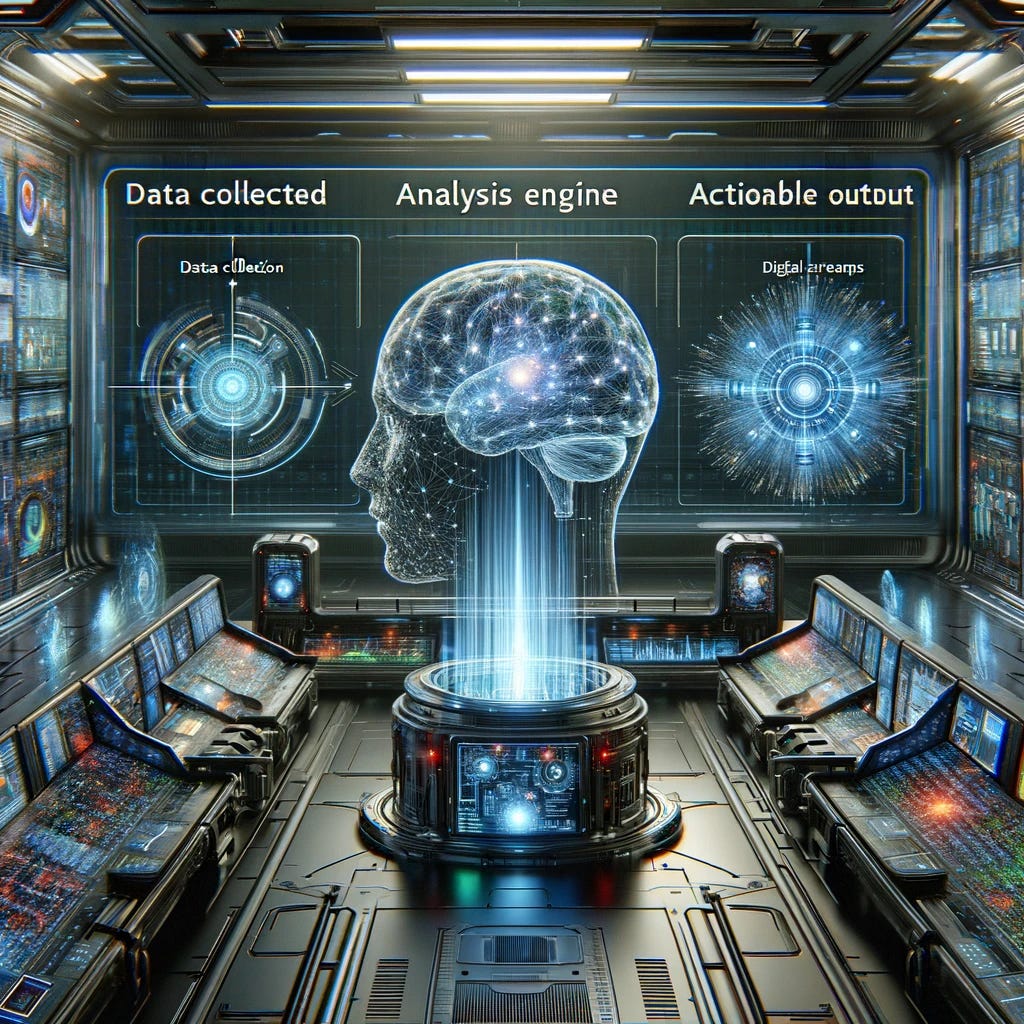
Data Collected - Analysis Engine - Actionable Output
Cybersecurity technologies, like all software, adhere to a basic framework encompassing data intake, data analysis, and the generation of actionable output. For instance, a traditional application security static code analysis tool ingests the binary or source code of applications, conducts an analysis to detect vulnerabilities, and then produces a list of exposures with remediation instructions. This framework can describe nearly any cybersecurity technology on the market today. While it's a nuanced and focused version of general software theory, it's beneficial to consider cybersecurity within this framework as it offers a means to differentiate between technologies.
Historically, cyber companies have distinguished themselves in at least one aspect of this framework when building their products. They often highlighted a "superior analysis engine" as the primary reason for being a more effective solution in detecting attacks or attackers. This approach led to a point-solution strategy in cybersecurity, where products excelled in resolving specific issues but lacked integration with other siloed technologies. As a result, "defense in depth" became the expected norm.
The popularity of defense in depth surged as enterprise cybersecurity teams amassed various solutions in pursuit of the ideal combination of detection, protection, and response technologies. This method, akin to needing a better mousetrap (analysis engine) that targets only mice while ignoring other creatures, propelled the cybersecurity market towards a focus on identifying more vulnerabilities and exploits rather than mitigating risk. To effectively reduce risk, the value proposition of products must evolve beyond mere issue detection to encompass other elements of the foundational framework.
API and Cloud Adoption Drive The New Security Data Fabric
With the growing adoption of cloud infrastructure, software as a service (SaaS), and API-based communications, our access to data has significantly expanded. Data is now omnipresent and readily accessible via APIs.
Transitioning workloads to the cloud removed them from traditional data centers, placing them in environments where every aspect, including configuration and current state data, is accessible through APIs. The rise of SaaS usage transferred corporate data into the hands of third parties, offering API-based access in return. Moreover, the explosion of API communication patterns, as applications were segmented into smaller components to exploit cloud-native services, gave rise to microservices and service mesh architectures, all underpinned by API communication models.
In today's world, we are inundated with data, possessing the capability to access extensive enterprise information in real-time, often with minimal programming expertise. The common saying, "There's an app for that," has evolved to "There's an API for that!"
Context Is The Next Wave of Oil
Isolated data fragments are limited in utility. Data's value multiplies exponentially when numerous pieces are combined, providing insights unattainable in isolation. Consider a scenario where your car has a flat tire and is involved in an accident on the same day. One could infer that the flat tire either caused or resulted from the accident.
When two or more pieces of data are near each other in logical proximity, we may gain additional insights and value that couldn’t be perceived when the data points were viewed in isolation. This is context, and context is king. Taking multiple data points and looking at them holistically to make more competent observations is contextual awareness, which humans are really good at.
We live in a world with more data and, thus, more context than ever. In addition to quantity, this breadth and depth of data is available programmatically, increasing the speed at which systems can consume and analyze it to create additional context. More context begets more data, so the virtuous cycle continues as analysis creates and builds more and more contextual knowledge, feeding on itself as the gravitational pull between the raw data and the contextual output becomes more intense. The pace of contextual creation is gaining speed, and there is no way to stop it.
Context has become the new oil. As technology and software companies devise systems that amass vast data collections, the contextual insights gleaned from analysis generate a network effect for the owning businesses. Context transforms into the high-octane fuel powering the engines of artificial intelligence and future computing systems.
Improved Analysis with AI-Derived Contextual Decisions
Humans excel at drawing connections and inferences from discrete data points. We are adept at observation and recollection, enabling informed and intelligent decision-making. However, humans are not as efficient in the speed of analysis. Becoming a subject matter expert involves years, sometimes decades, of focused study and experience, a gradual ascent up "knowledge mountain."
In contrast, computers excel in processing speed, designed for swift execution of processes and data analysis. The advancements in artificial intelligence have enabled computing systems to process vast amounts of data and solve complex problems in a fraction of the time required for human analysis. What might take a human a decade to learn, AI can master in mere weeks or months.
Simply put, artificial intelligence involves processing massive data sets, posing context-based questions in natural language, and rapidly deriving accurate answers. As AI's analytical capabilities evolve with our expanding data access, context will multiply exponentially. Over time, AI will become more adept and intelligent, drawing inferences not just from raw data but from the amalgamation of multiple contextual elements, now seen as a data superset.
In this equation, Context + Context = Consciousness. Applying these analysis techniques to cybersecurity, as previously discussed, suggests that cybersecurity technologies are on the brink of a revolutionary capability to observe and protect our cyber universe like never before.
Automated Workflows On Accurate Data
In cybersecurity, there's a prevailing belief that automated solutions to security issues are risky, as errors could compromise services, networks, or applications, eroding trust in both the automation and the security team. Historically, this caution was warranted, as security automations were not context-aware and relied solely on raw data, lacking the nuanced decision-making akin to human consciousness. The risk of technology-driven decisions was deemed too high.
However, today's landscape is different. Our source data comprises analyzed context, offering a more precise foundation for decision-making. Our analysis engines now emulate human consciousness through AI, utilizing a very rich data set. Furthermore, our outputs are expected to yield unparalleled data comprehension and accuracy. If these factors hold true, we can automate fixes with a sufficiently low-risk level, making automation preferable to human intervention.
The New Cyber Platform
To reiterate: "The difference between traditional cybersecurity products and modern cybersecurity platforms is the incorporation of context (data) and AI to enable more intelligent and accurate decisions."
The question isn't if we can develop a cybersecurity platform that emulates human behavior and intelligence, executing its recommendations in real-world scenarios, but when? As AI and contextual understanding evolve alongside the proliferation of APIs, so too does our intelligence's richness. Gradually, we will build trust in the system's answers to complex questions, allowing for autonomous corrections. This progression could mark the beginning of a significant advantage in the fight against cyber attackers. The barriers separating technologies, people, processes, and data will crumble, granting us a comprehensive view of the cybersecurity context and, hopefully, a real chance at success.
...until, of course, attackers begin to leverage the same contextual insights.





Thanks for putting your vision on the future of security into words Tyler! Very interesting read.
What you are describing sounds as the security holy grail to me: see across the whole environment, find the issues, prioritise, get to the root cause and finally fix them automatically.
That sounds really great!
Then I use copilot/chatgpt in my daily work, and find myself arguing with it about some obscure (in the best case) or obvious thing it missed, which changes the whole dynamic of an issue. Maybe the tool is good and I’m just using it wrong. Maybe we’re on a power law with AI capabilities and I’m not able to extrapolate well. I’m not sure.
To be clear, I’m not arguing AI/LLM’s aren’t going to be the thing in cybersecurity for the next few years. But what you’re describing does seem like a lot to ask of it.
Especially with how it seems to have the tendency to be right in 90% of the cases, but spectacularly wrong in 10% of the cases.
Instead, I think it’s an additional tool in our arsenal, to be used on top of our other tooling. We have potential security issues where we don’t have any context (for example: a code linter looking at string concatenation in sql queries), where the fix is so cheap/quick/easy, it is a no brainer.
I wouldn’t start relying on a finicky AI, if I have a stupid tool which works consistently in 100% of the cases.
So anyway, this comment turned out to be a “right tool for the job” manifest… :-) I’m excited to see what the future holds!
I enjoyed this post. I feel optimistic that Microsoft's Security Copilot may end up being a good example of some of the progression you've highlighted here.