The Cyber Why: What We Read This Week...
... and why you should too! (09/20/23)
Oh man, we read a lot this week. For almost nine days, I have been completely enthralled by the ransomware drama playing out at some of the world’s top mega-resorts and casinos. Talk about a damaging attack. Also of significance this week are TOS changes to support AI growth, a slowing down in Israeli cyber investing, cashing in on the AI bubble, a 38TB MSFT leak, and more! Grab your afternoon coffee and check out this week’s The Cyber Why!
Featured Sponsor - Next DLP
Stop Data Exfiltration & Expose Risky Behavior
The Reveal Platform by Next DLP instantly identifies risk, including malicious insider behavior, so you can quickly implement policies to secure sensitive data. You'll balance blocking with point-of-risk user training, all while your business keeps humming. Born and built in the cloud, it's data loss prevention at the heart of a modern security ecosystem. nextdlp.com
Gambling on Ransomware - House Edge at Zero
Massive MGM and Caesars Hacks Epitomize a Vicious Ransomware Cycle (Wired)
MGM, Caesars Face Regulatory, Legal Maze After Cyber Incidents (Dark Reading)
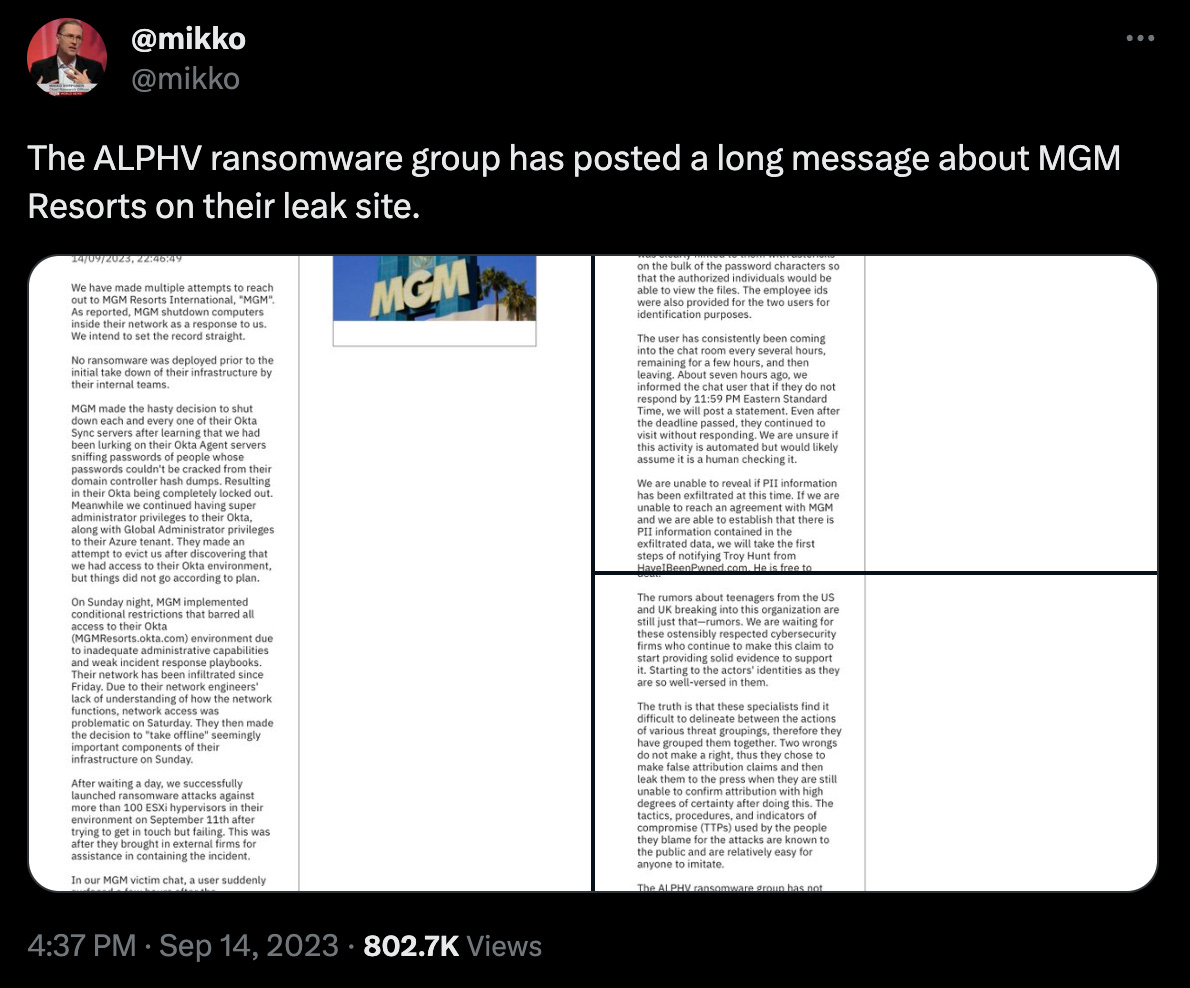
Ransomware group steps up, issues statement over MGM Resorts compromise (Malware Bytes)
Hackers who breached casino giants MGM, Caesars also hit 3 other firms, Okta says (Reuters)
MGM losing up to $8.4 million a day due to cyberattack, analyst says (Las Vegas Review-Journal+
UPDATE: 'Cybersecurity issue' takes down systems at MGM Resorts, affects gaming operations (CDC Gaming Reports)
Our opening story is the massive compromise of both mega-resort and casino companies MGM and Caesars- and this one is a BIG ONE! MGM first went offline on the 11th, including losing the ability to check in guests, swipe credit cards, unlock doors to rooms, take reservations, track comps, and presumably MUCH more! At one point, MGM was believed to be losing over $8M a DAY in revenue. That wouldn’t be a tremendous problem if things were fixed quickly, but we are nine days into the attack, and they are just now getting things back online. Caesars chose the other route and paid $15M upfront to the ransomware gang to avoid the outage. It’s believed that Okta technology plus social engineering were critical components of the breach. Both companies will face legal and regulatory issues regarding this breach. Time will tell whether paying the ransom (Caesars) or holding out (MGM) had a better financial result for the casinos. One thing we know for sure is that, in this instance, the odds aren’t in the house’s favor!
Ignore The TOS Change - Get Me a Latte!
A long list of companies have started to modify their terms of service to include using your data in the generation of their current and future AI models. X, Instacart, Meta, Zoom, Rev, and many more have added stipulations that they can and will use all data they can get their hands on to improve their AI-based services. I can’t say that I’m surprised at all. The more data the AI engines can see, the more accurate they can be in the predictions and generative outcomes they create. Every business should be adding these phrases to their terms of service. The real question is how the public will handle this in the future when they realize that they have given away every single scrap of privacy they once had. My bet is they won’t care. When their unattended virtual assistant orders the correct Starbucks drink and has it delivered to the location, they will be at around 2:30 PM when their blood sugar usually dips without them having to ask for it - they will be okay with the data collection.
Israeli Cyber Investments and Exits Slow
Israel’s Startup Funding Drops As Its Famed Cyber Sector Takes A Hit (Crunchbase)
The critical piece of this article isn’t the headline or the mediocre analysis. The exciting parts are the graphs showing how much the cybersecurity investment world in Israel has slowed down. I’m sure that a large piece of the slowdown is the effect of the over-investing that occurred in the last few years, but it is interesting to see that even the famed Israeli cyber mafia has had to “slow their roll” due to the downturn in the US and the global economy. Who says that cybersecurity technologies are recession-proof?!
A Framework To Cash In On Bubbles
Why AI Stocks Aren’t In A Bubble (Goldman Sachs)
Here’s How Index Ventures Is Investing In An Era Where ‘Every Company Will Have AI’ (Crunchbase)
This article by Goldman Sachs takes a shot at debunking the idea that AI stocks are in a bubble. While I’m not sure I fully agree with their reasoning, the article has a killer framework that is used to help identify where money can be made in the AI revolution over the next decade or so. It’s called the PEARL framework. They describe companies in the framework like this:
Pioneers are the innovators, and they include the early winners.
Enablers facilitate the innovators and help to commercialize the technology.
Adapters are companies in other industries that change their business models to use the new technology effectively.
Reformers are typically new market entrants unencumbered by legacy costs.
Laggards may have a dominant incumbent position in an industry, but, for whatever reason, react slowly and fail to keep up with new innovations.
The article goes into MUCH more detail, so go read it. To date, most people have invested in picks and shovels (Enablers) such as NVDA and ARM. I have been personally most excited by the Adapters who will take these concepts and reinvent their respective markets. At the end of the day, I’m sure many of the Pioneers (Google, OpenAI, Facebook, and others) will do well, but I can’t wait to see the broader impact over time that AI brings to how we live our lives.
Oops… I Did It Again! MSFT Blobs Are Leaking Once More. - Rick Pick!
38TB of data accidentally exposed by Microsoft AI researchers (Wiz)
Microsoft mitigated exposure of internal information in a storage account due to overly permissive SAS token (Microsoft)
Microsoft leaks 38TB of private data via unsecured Azure storage (Bleeping Computer)
Microsoft has had a rough go of it lately, much of which has been self-imposed. Earlier this year, a Chinese threat actor (Storm-0558) acquired a signing key to access sensitive MS Exchange and Outlook accounts by compromising a support engineer. This week, Microsoft and Wiz disclosed an accidental 37TB data leak via "an overly-permissive Shared Access Signature (SAS) token for an internal storage account." The data included backups of personal data, passwords, secret keys, and over 30,000 Teams messages. This exposure isn't the first leak of sensitive Microsoft data. Threat intel provider SOCRadar disclosed Azure Blob Storage leakage in October last year. #OOPSEC is a problem.
Quick Hits and Hidden Gems
More quick hits from the TCW crew! These articles didn’t make the cut for top billing, but we still found them fascinating. There are some real gems in here… go forth and read.
Musk says X will charge everyone to use the platform (Axios) - I think Elon spews this garbage out to gauge reaction to his batshit crazy ideas.
Google’s Bard chatbot can now tap into your Google apps, double-check answers and more (TechCrunch) - I immediately signed up for this one. So far, it’s intriguing but not all that useful. I’ll continue to research and get back to you!
FBI director urges private sector to lend help in cyber intelligence (CNBC) - It’s been the same shit for 20+ years. Urging is CLEARLY working well! </sarcasm>
Generative AI’s Biggest Security Flaw Is Not Easy to Fix (WIRED) -Indirect prompt injection attacks are one of the most significant risks in AI!
CrowdStrike confirms its Bionic.ai acquisition for $350M today (TechCrunch) - The ASPM space might be TOO hot to become a real market. Acquisitions are likely to happen fast and furious!
AI and Cybersecurity: An In-Depth Look at LLMs in SaaS Software (Cyber Builders) - This is a really inciteful series by Laurent Hausermann. Check out all three articles.
Clorox results show ‘material impact’ from cyberattack (Cybernews) - Eeep another materially impacting breach. This one shut down production, causing shortages. OH NO!
If you’ve made it this far, you either found our musings at least semi-entertaining, OR you enjoyed the pain and kept going regardless. No matter how you made it to this point, you should know that we appreciate you. Please do us a solid and share The Cyber Why with your friends. We would love to reach a bigger audience, and referrals are how we do it. Help us out, and we’ll see you next week!